Quick Read
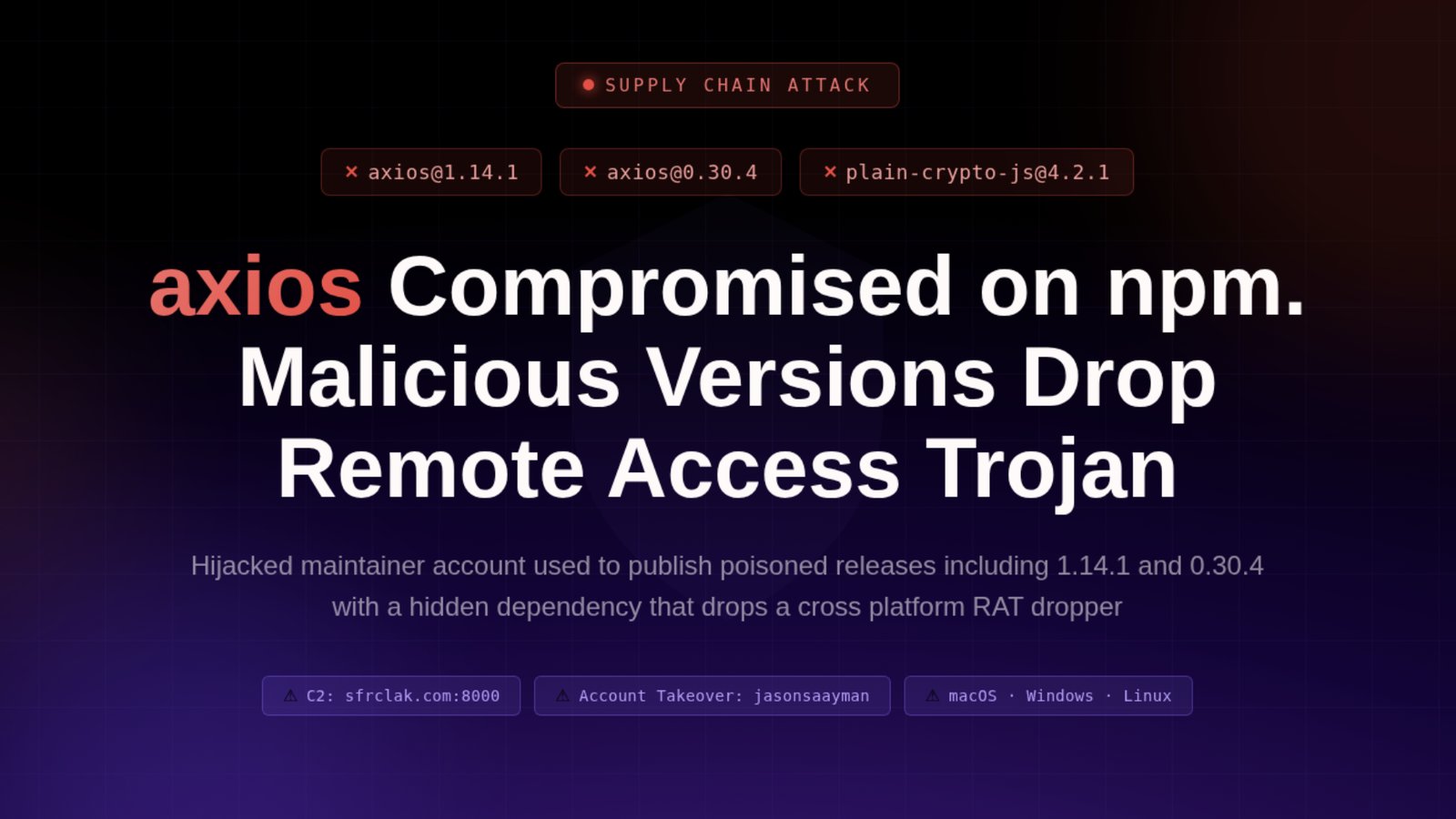
- Malicious versions axios@1.14.1 and axios@0.30.4 were live for roughly three hours on March 31, 2026.
- The attack deployed a cross-platform RAT that self-deletes after execution to evade detection.
- Systems that installed the affected packages must be treated as fully compromised and require immediate credential rotation.
On March 31, 2026, the global software supply chain faced a significant security breach after the npm registry account of the lead maintainer for Axios—a JavaScript library with approximately 100 million weekly downloads—was hijacked. The attacker used this access to publish malicious versions of the library, specifically axios@1.14.1 and axios@0.30.4, which contained a hidden dependency designed to execute a Remote Access Trojan (RAT) immediately upon installation.
Understanding the Axios Supply Chain Compromise
The attack, which remained active for approximately three hours before npm security teams intervened, bypassed standard CI/CD protections by targeting the registry directly. According to reports from Socradar and Help Net Security, the malicious versions included a dependency named plain-crypto-js@4.2.1. This package utilized a postinstall script to drop platform-specific malware onto Windows, macOS, and Linux systems. Crucially, the malware was designed to self-destruct after execution, wiping its own malicious files and replacing them with clean configurations to evade basic forensic inspection.
Assessing the Scope and System Stakes
The sophistication of the operation suggests a calculated effort rather than opportunistic crime. By targeting both current (1.x) and legacy (0.x) branches of Axios, the adversary maximized the potential reach across diverse development environments. Tom’s Hardware notes that the dropper established command-and-control communication within seconds of the npm install command. Because the library is a core component in countless web applications, backend APIs, and CI/CD pipelines, the breach poses a severe risk of credential harvesting, source code theft, and lateral movement within corporate networks.
Immediate Remediation and Security Verification
Security researchers advise that any system that executed npm install during the window of compromise (roughly 00:21 to 03:15 UTC on March 31, 2026) must be treated as fully compromised. Organizations should immediately isolate affected machines, perform a clean re-image, and initiate a comprehensive rotation of all secrets, including cloud IAM roles, SSH keys, and API tokens that were accessible from the impacted environment. Developers are urged to scan their package-lock.json files for the malicious package signatures and utilize provided community scripts to verify system integrity.
The speed and stealth of this incident underscore a critical vulnerability in the modern reliance on automated dependency resolution. By bypassing build provenance—a feature that would have flagged the lack of legitimate GitHub Actions metadata—the attacker demonstrated that even widely trusted, open-source building blocks can be weaponized to achieve near-instantaneous global distribution of malicious payloads.